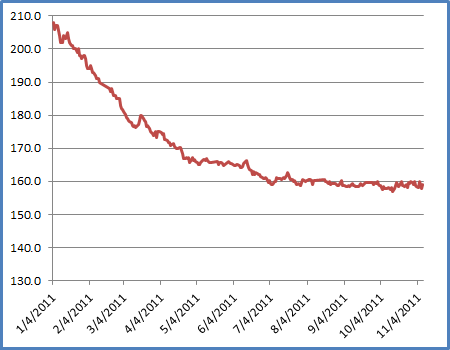
I've had a lot of questions from a lot of people over the past few months about my extreme weight loss this year, so I thought that I'd post a few words to explain how I accomplished that. To put things in perspective, between the start of January, 2011, and the end of June, 2011, I lost 50 pounds (22.7kg). What's more, I've kept the weight off for an additional five months.
Here's the story behind all of that.
Falling Apart (or Bursting at the Seams)
First of all, I knew that I was really overweight.
In December of 2010 my weight reached 210 pounds. As I had watched my weight grow over the years, I had a series of "superhero" names that I called myself:
- First I was "Porky Boy."
- Next, I was "Fat Man."
- Later, I was "The Obese Avenger."
- I was rapidly growing into "The Morbid Marauder."
I made all the usual comments at my own expense:
- "I'm in shape - round is a shape."
- "I have six pack abs - I'm just keeping my six pack insulated."
- "I'm watching my weight. It keeps going up, but I'm watching it go up."
I went into something of a denial phase - I started buying my pants from one particular store, because their brand of jeans were actually larger than their advertised size. So I felt better about the fact that I was wearing jeans that were advertised as size 36, when I was really wearing size 38 or larger. Even then I had a serious "muffin top" that would hang over the top of my jeans. I never tucked in my shirt in order to help disguise my condition.
I knew things were bad when a cab driver in Iquitos, Peru, charged an extra fare for my wife and me because he said that we were too fat. (Actually, he didn't say it, he pointed at me and gestured like I was a balloon inflating.)
But all joking aside, I knew that I was in trouble because my blood pressure had elevated to 170/120, which is dangerously high. (120/80 is normal.) I decided to start exercising, and in early January, 2011, I had barely made it 15 minutes into a workout before I thought that I was going to have a stroke. That's when I realized that I needed a doctor to help me get started.
With this in mind, I took a week off for vacation, and I spent most of that week visiting doctors. I saw a general practitioner who put me on medicine to control my blood pressure. I also saw a neurologist because of my frequent headaches, which were actually chronic migraines. (Undoubtedly due to the blood pressure.) I saw a bunch of other doctors for a variety of additional medical symptoms that I was experiencing, but for the sake of expediency I'll spare you the details.
To make a long story short, it seemed like I was falling apart.
Exercising and Counting Calories
Within a few days, the blood pressure medicine did the trick; I could keep my blood pressure low and complete a workout. For exercise, I bought a treadmill from NordicTrack that connected to www.ifit.com, which allowed me to track the distances that I walked each day. (Hey - if you're a geek, it shows up everywhere.) I bought several series of documentaries on DVD from the History Channel and the Discovery Channel, and I would watch those documentaries while I walked for an hour or so.
I also created a measured walking path through buildings 16, 17, and 18 on Microsoft's main campus; these buildings are connected by glass-covered walkways, so I could still walk when the weather was nasty outside. My walking trail was around three-quarters of a mile long, and it took me about 15 minutes to walk it. It's interesting, because I had never noticed before how many people put out cookies and candies in the hallways. I could ignore all of it - but it's kind of funny that I hadn't paid much attention before.
I have to stress that I did not do a lot of exercise to lose the weight - I mainly started counting the calories for everything that I ate, and I tracked those calories diligently. (I'll explain more about that later.)
My general method of calorie counting was to calculate my Resting Metabolic Rate (RMR), then I would subtract 1,000 calories from that. Whatever was left was the calorie count that I was allowed to eat for the rest of the day.
Here's what that looks like:
There are lots of websites that will help you find the calories for meals, although I liked http://www.livestrong.com/myplate/ the best. I also created a OneNote file that I could read on my SkyDrive and through the Office application on Windows Phone 7 where I listed the calories for the foods that I eat the most; this made it easier to keep track.
It got to the point where I would say to myself, "I really want to eat those M&M's, but I'll have to work out later to burn off those calories." I also learned to browse to a restaurant's website before going out to dinner and picking my meal by calculating the calories ahead of time. In order to help cut down on craving, I stocked my desk with a bunch of 90-calorie snack bars. Those or a bowl of oatmeal became my daily breakfast, and in between my reduced-size meals I would have a snack bar.
I should stress that I did not give up the foods that I like - it may be healthier to do so, but I don't think that's sustainable for some people. (That includes me.) I would still have pizza, or a Qdoba burrito, or a burger from Five Guys; but I would simply have less of everything. If I had a burger somewhere, I'd skip the fries. I'd only have a couple slices of pizza, instead of eating the whole pizza. Keeping the weight off is about sustainability - and eating food that I like in moderation works for me.
I should also point out that at no time was I actually hungry during my weight loss period; that's where the snack bars paid off. Instead of being famished when lunch or dinner rolled around, I could get by with a simple meal of 300 or 400 calories and be satisfied with that.
As long as I stuck faithfully to counting my caloric intake on a daily basis, my weight and the inches around my waistline started to recede.
Losing Weight (while Undoing Years of Abuse)
After five weeks my weight had dropped 20 pounds; my pants were fitting a lot looser, and a few people started to take notice. This was fuel for my self-motivation; the fact that someone could actually see that I was losing weight was great, and it made everything worth the effort. Of course, I still weighed 190 pounds, which was 25 pounds overweight, so any elation was short-lived.
As an added bonus, my weight had dropped so much that I no longer needed the medicine to control my blood pressure. In fact, the medicine was making my blood pressure way too low. One day I finished a workout and I felt a little light-headed. So I took my blood pressure, and I discovered that it was 80/60, which is low enough to pass out. (I stopped taking the blood pressure medicine immediately.)
After losing 30 pounds it was kind of cool - I could tell by looking in a mirror that my face was thinner, and more people started mentioning that it looked like I had lost some weight. But I was still faced with the knowledge that even though I had lost 30 pounds - which was significant for only two months' worth of effort - I still weighed 180 pounds, which put me 15 pounds into the "Overweight" weight range.
When I had lost 45 pounds in May, 2011, I hit my initial weight loss goal. This put my Body Mass Index (BMI) at 25, which was the high end of the "normal" range. To celebrate, I took a break from actively losing weight for a couple weeks, and I went into maintenance mode. So for the next month I continued to count my calories, and I simply kept my weight at 165 pounds.
During my brief respite from active weight loss, I had a follow-up appointment with the same doctor with whom I had met in January. He was shocked when he saw me, and he asked me what had happened. I replied that I didn't want high blood pressure, sleep apnea, and heartburn for the rest of my life. More than that, I didn't want to have to worry about a stroke or heart disease. The doctor gave me a clean bill of health, and a couple of weeks later I started losing weight again.
By the end of June or the beginning of July, I had hit my ultimate weight loss goal of losing 50 pounds, and I've kept it off since then. My waistline went down several sizes, so I have had to change my daily wardrobe through several successively-smaller sets of jeans, which was a great feeling.
Here's what my weight loss chart looks like for the year of 2011 (so far):
The After Effects
First and foremost - I feel great. I have no more migraines, I sleep better, my heartburn is gone, my blood pressure is back to normal, and I have lots more energy.
I'm also in much better shape. In fact, my wife and I walked the Leavenworth Half-Marathon in October, 2011; and here is a photo of the two of us crossing the finish line:

I thought that it might be good to show a set of "before and after" photographs, just so you can see the difference that 50 pounds can make:
 |
 |
| December, 2009 |
July, 2011 |
(My thanks to Rebecca Calvo for the photos!)
How Anyone Can Lose Weight
A while ago I posted some weight loss information to Facebook in order to answer a few people's questions about my experiences; since I keep my list of friends on Facebook pretty small, I thought that I'd share some of that information here. But I also wanted to make it a little more up-to-date with some additional information.
My secret to weight loss? Microsoft Excel.
Well, it's a little more than that - but it's mostly just counting my calories and making sure that I eat 1,000 calories less per day than my Resting Metabolic Rate (RMR), for which I use Mufflin equation:
- For Men: (10 x w) + (6.25 x h) - (5 x a) + 5
- For Women: (10 x w) + (6.25 x h) - (5 x a) - 161
Where:
- w = weight in kg
- h = height in cm
- a = age
I converted this equation into the following complex Excel formula:
=((10*(B2/2.2))+(6.25*(B3*2.54))-(5*B4)+IF(B1="Male",5,-161))*IF(B5="Extremely Active",1.9,IF(B5="Very Active",1.725,IF(B5="Moderately Active",1.55,IF(B5="Lightly Active",1.375,1.2))))
Where:
- B1 = Male or Female
- B2 = Weight (in pounds)
- B3 = Height (in inches)
- B4 = Age (in years)
- B5 = Activity Level (Sedentary, Lightly Active, Moderately Active, Very Active, Extremely Active)
To make things easier, I created the following spreadsheet to help me track my calories:
Geeky Bob's Weight Tracking Spreadsheet
If you want to use it, here's how it works - there are two worksheets in the spreadsheet:
- On the Settings worksheet, you enter your weight, height, age, activity level, and the number of pounds that you want to lose in a week. You should only shoot for a maximum of two pounds a week; anything more is really unsafe, and your body will respond by slowing down your metabolism to conserve resources.
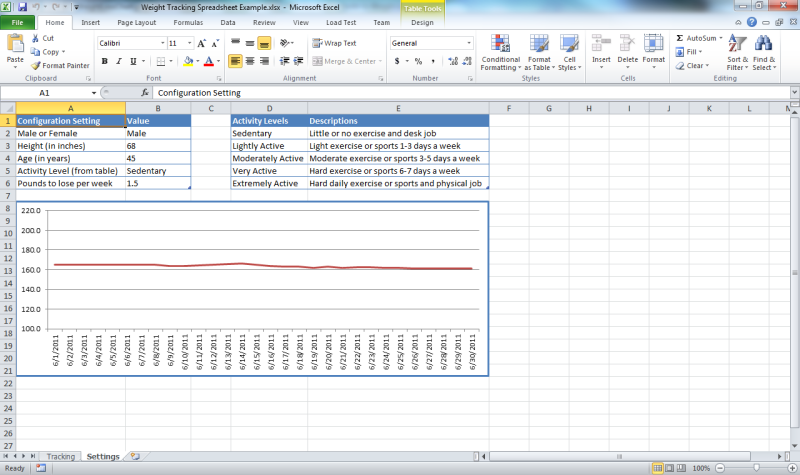
- On the Tracking worksheet, you enter the date and your weight, and the spreadsheet uses this information and the information from the Settings worksheet to calculate your Body Mass Index (BMI) which should be below 25, and your Resting Metabolic Rate (RMR) which is the number of calories that your body burns just to keep you alive.
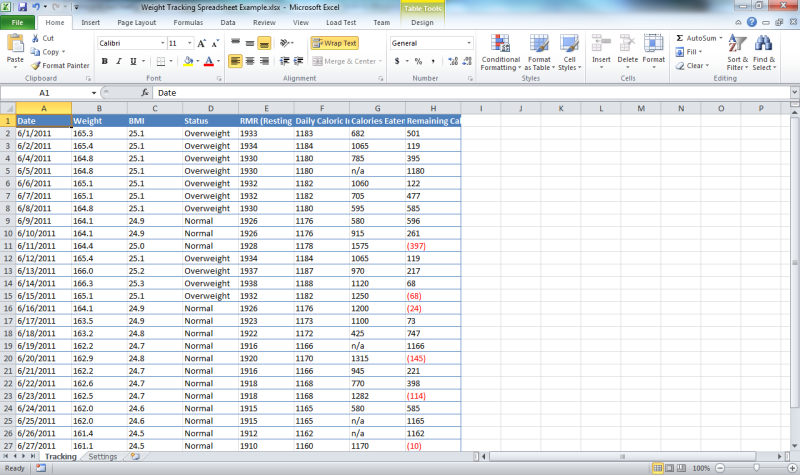
The remaining columns in the spreadsheet will tell you the number of calories that you can eat based on your weight loss goal. As you enter the number of calories that you have eaten (by using a formula like "=100+200+300") the spreadsheet will let you know how many calories that you have remaining for the day. As long as you keep your remaining calories above zero, you should be losing weight.
So there you have it: Microsoft Excel is the Geek's Guide to Weight Loss.
;-]